If you’re in the technology infrastructure space, chances are that you have heard of SSE (software-defined environments) and SASE (secure access service edge).
We hear about these buzzwords being flung around regularly, but what do they mean? After all, especially when it comes to security solutions for your business or organization, knowledge is power.
In this post, we’re going to draw a direct comparison between SSE vs. SASE; outlining clear differences between the two so that by the end of our showdown.
There’s no doubt left as to which may be most beneficial for your team’s needs!
SSE Vs SASE: The Overview
Security Services Edge (SSE) is a comprehensive network security services solution that unites numerous cloud-based security services that were previously consumed independently.
SSE simplifies management and lowers maintenance costs by combining all components into a single platform, including a single management platform, a single agent, and a single network-as-a-service.
With SSE companies may connect to a single secure cloud network-as-a-service where they have access to both physical and cloud resources.
In the hands of IT, SSE allows more comprehensive and agile networking, including work-from-home and work-from-office employees, linking various office networks.
And providing a single multilayered defense against cyberattacks that keeps users and resources—both on-prem and on-cloud—fully safe.
SSE is a game-changer because of its cloud-based, unified, and simplified security capabilities, all of which may improve productivity, security, and the bottom line for any business.
As a result of Covid and the “Decentralized Workplace,” many offices are now either completely or partially vacant.
SSE Vs SASE: The Differences
SASE, a.k.a. the Secure Access Service Edge, was initially defined by Gartner in 2019 and may sound similar to SSE. Indeed it is.
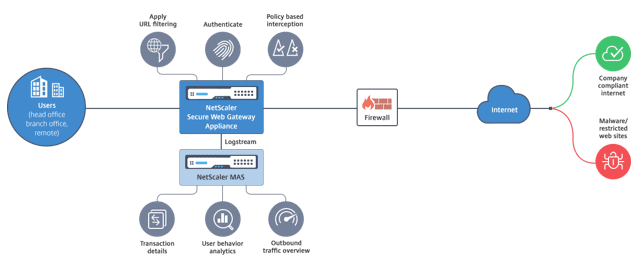
Cloud-based security services like Zero Trust Network Access, Firewall as a Service, Secure Web Gateway and Cloud Access Security Broker are all part of SSE, which is the SASE model’s network security side.
Non-security WAN services provided by SASE fall under the WAN Edge Services category. Services include SD-WAN, WAN Optimization, QoS, Routing and more.
Due to the new segmentation of WAN and security edge services, this architecture allows enterprises to more easily transition to the cloud, increase mobility while maintaining security, and provide a better user experience.
IT professionals can learn more about the various SASE suppliers’ products and services.
Some vendors—like Perimeter 81—offer experience in cloud networking and secure access, while others have a past record of WAN services and gear.
What’s the Big Deal about SSE?
Because of the record amount of remote and hybrid employees in today’s contemporary workforce, more and more resources are being moved to the cloud.
Fewer than eight percent of organisations use computer resources that are totally or largely on-premises, while almost half (47 percent) do so on the cloud.
With SSE’s software-defined architecture, network administrators can set up and operate networks from a distance, all while defining user-specific access restrictions based on certain types of devices, user roles, and other detailed criteria.
Without the need for any additional hardware or intensive management, SSE provides comprehensive network visibility and control from a single admin interface.
SSE and The Cybersecurity Experience Platform
With its revolutionary ease-of-use and radically simple user interface, Perimeter 81’s Cybersecurity Experience Platform (CSX) is the first platform to simplify SSE with five principles:
Instant Deployment, Unified Management, Full Visibility, Integrated Security and Unwavering Support.
The CSX Platform helps enterprises to protect their hybrid cloud and on-prem network with:
- To precisely regulate who has access to specified network resources and when Zero Trust Network Access (ZTNA) is used.
- Microsegmenting user access to resources with FWaaS (Firewall as a Service).
- Security regulations are enforced by the Secure Web Gateway (SWG).
- Device Posture Check (DPC) to check the authenticity of devices during login to avoid malicious attacks.
- Clientless Zero Trust Application Access (ZTAA) to enable partners and contractors to safely access particular apps from unmanaged devices.
- Monitoring Dashboard to discover abnormalities and take remedial action.
However, Perimeter 81 is more than just a collection of useful options. For our clients, it’s all about providing an unmatched experience—an unmatched cybersecurity experience.
Features, usability, and customer service are all top-notch.
But I’m not the only one who says that. As stated in Forrester’s Q3/2021 ZTNA New WaveTM, “Perimeter 81 reference customers are among the most enthusiastic of those included in this evaluation,”.
They praise the vendor connection, support and desire to develop the product quickly.”
If you’re ready for SSE, we’re ready to help.
Pros and Cons: SSE vs SASE 2024
SSE Pros |
SSE Cons |
| Increased agility and flexibility | Costly to implement and maintain |
| Quickly respond to changes in demand | Vulnerable to cyberattacks |
| Improved scalability of software-defined environments | Difficult to troubleshoot issues |
| Better security, eliminate vendor lock-in, reduce costs | |
| Easily add or remove resources as needed |
SASE Pros |
SASE Cons |
| Increased flexibility, simplicity, and security | Difficult to integrate with existing security solutions |
| Ability to access both on-premises and cloud-based resources from anywhere in the world | Costly for small scale organizations |
| Advanced security features | |
| Lower costs |
Conclusion: SSE vs SASE 2024
With SASE emerging as the clear winner in this year’s SSE vs SASE showdown, organizations should think about how existing architecture like SSE may put a strain on employees & endpoint users when it comes to their security & performance.
There’s no doubt that software defined solutions are the future of corporate networking.
By leveraging the power of cloud-based technologies through service like SASE, organizations can ensure better end user experience whilst staying secure and compliant with regulations.
It is essential to carefully consider the cost effectiveness, functionalities and potential pitfalls that come with either technology. Every company has different needs when it comes to their network.
That being said, it seems clear that the success or failure of their digital transformation will heavily depend on informed decisions related to this important choice.
It is always wise to stay abreast on current industry trends, evaluate possible solutions and speak to experts before making an ultimate decision.