Have you ever wondered “Does VPN Protect Your Online Privacy?” or “Does VPN really keeps your online activities private?” Well, I was curious too, especially with all the talk about internet safety these days.
So, I decided to dig in and find out if using a VPN is the secret to keeping my online life just between me and my screen.
Virtual private networks, generally known as VPNs, are gaining popularity as a security solution for both businesses and individuals. Will using a VPN protects your online privacy?
A VPN acts like a hidden tunnel for your internet connection. It hides your real location and encrypts your data, making it tough for anyone to track what you’re doing online. But is it foolproof?
Let’s explore how a VPN works to protect your online privacy and if it’s the ultimate shield we’ve all been looking for.
Why Is VPN Important?
Using a Virtual Private Network (VPN) provides online anonymity and privacy. It disguises your IP address, making it impossible for your ISP to track your online activity.
By establishing an encrypted connection between the sender and the receiver, Virtual Private Networks (VPNs) give the impression of being in a different place.
By masking the sender’s IP address, VPNs make it incredibly difficult for eavesdroppers to access your online conversation, which is one of the main reasons why they are so popular.
VPNs are widely used by enterprises to facilitate remote work since they establish a secure, encrypted connection to the corporate network. However, your employer could still see what you’re up to online.
What else can a VPN do?
Does Private Browsing Offer True Privacy?
You may wonder, “Is a VPN necessary if I already use my browser’s private mode for browsing?”
Modern web browsers come equipped with a privacy feature known as private browsing. This function allows users to navigate the internet without recording their browsing history, search queries, and temporary data such as cookies.
Private browsing modes are supported by leading browsers, including Apple Safari for Mac and iOS devices, Google Chrome’s Incognito mode, Mozilla Firefox, Opera, and Microsoft Edge with its InPrivate Browsing feature.
While private browsing modes prevent the storage of data on your local device or computer, they don’t fully shield your online activities from your Internet Service Provider (ISP) or protect against third parties who might be able to observe your browsing sessions.
These entities can potentially exploit vulnerabilities in your operating system.
Therefore, private browsing offers limited privacy and does not substitute the comprehensive protection a VPN can provide, which encrypts your entire internet connection and hides your online activities from ISPs, cyber threats, and unwanted surveillance.
How Secure is a VPN?
Image credits: Pixabay
The security of a VPN (Virtual Private Network) involves understanding its functions and the various factors that influence its effectiveness.
A VPN enhances online privacy and security by creating a private network from a public internet connection. It masks your internet protocol (IP) address, making your online actions virtually untraceable.
Moreover, it establishes secure and encrypted connections to provide greater privacy than even a secured Wi-Fi hotspot.
How to Ensure Online Anonymity: Use a VPN
The best way that you can make sure all of your browsing data is kept private is through the use of a VPN. A Virtual Private Network essentially uses a secure server hosted at a remote server as a proxy for all of your internet traffic.
This means that although you will be using the internet as normal, anyone spying on you will only be able to see that you are connected to a VPN and nothing else.
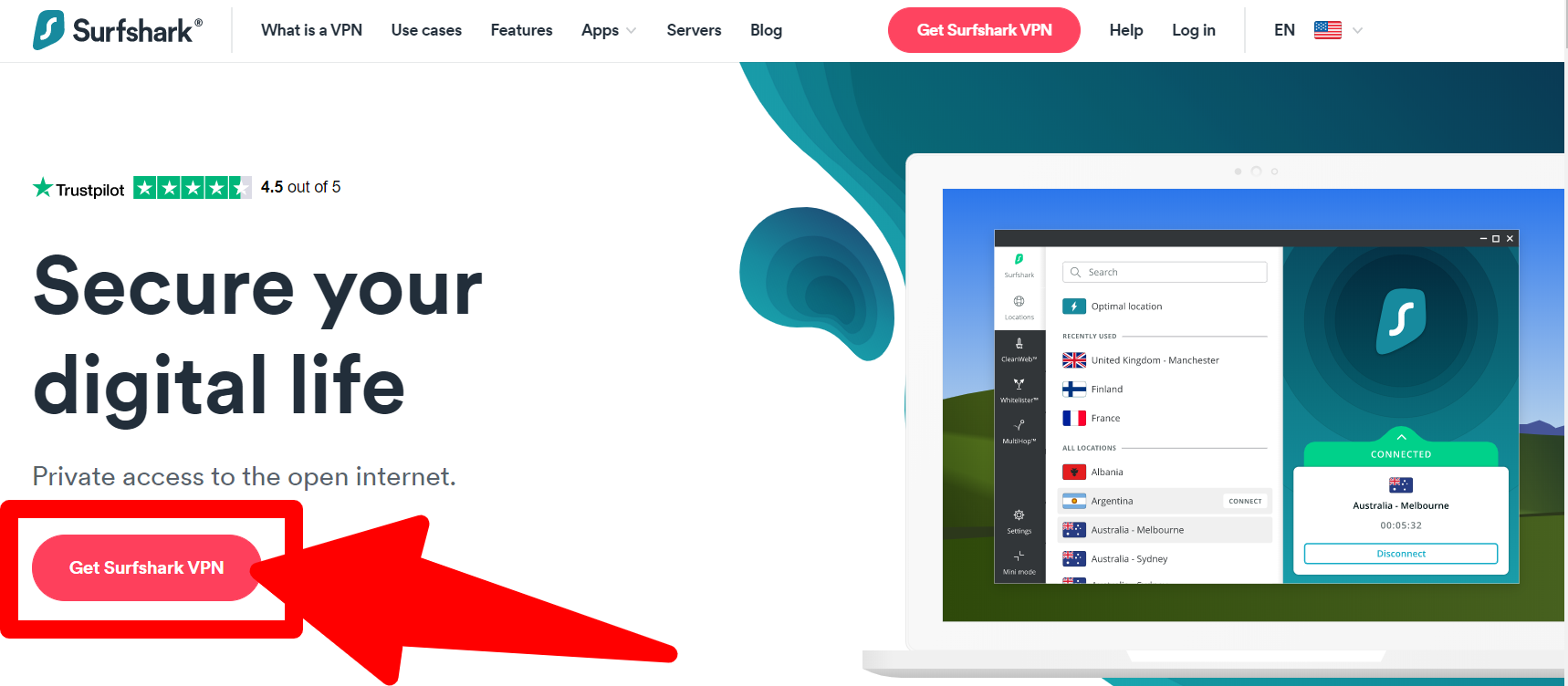
I recommend you use Surfshark since it provides the most secure browsing experience when compared to all of the other VPNs in the market.
Surfshark is not set up in fourteen eyes country, and it has all the features that make a VPN safe e.g. Encryption, Kill-switch, and DNS leak protection.
Do not worry, using a VPN is completely legal and you will not run into any problems whatsoever. All a VPN does is have your internet connection to a remote server.
Since anyone who is spying on you is unable to gain access to the remote server itself, they are unable to see which websites you are visiting.
Reasons To Avoid Free VPNs:
Image credits: Pixabay
Free VPNs might seem like an attractive option for enhancing online privacy and accessing geo-restricted content without a financial commitment.
However, the adage “you get what you pay for” often applies, especially when considering the safety and privacy implications of using free VPN services. Here are several reasons why free VPNs may not be safe:
FAQs About Does VPN Protect Your Online Privacy in 2024?
👉Can a VPN make me anonymous online?
A VPN greatly increases your privacy by hiding your IP address and encrypting your data, making it difficult for third parties to track your online activities.
👀Does a VPN protect my privacy on public Wi-Fi networks?
Yes, one of the primary benefits of using a VPN is that it encrypts your internet connection, which is especially important on public Wi-Fi networks. These networks are often unsecured, making it easy for hackers to intercept data. A VPN prevents this by ensuring that even if your data is intercepted, it cannot be deciphered.
🤷♀️Can websites track me when I use a VPN?
A VPN can prevent websites from tracking your real IP address, but websites can use other methods to track you, such as cookies, browser fingerprinting, or login information. To enhance privacy, use browser privacy modes or extensions that block trackers, and regularly clear cookies.
💁♀️Are there any online activities a VPN does not protect against?
Yes, a VPN does not protect against all forms of online threats. For example, it cannot protect you from clicking on malicious links, downloading malware-infected files, or falling for phishing attacks.
✔How do I choose a privacy-focused VPN?
Look for VPNs with a strict no-logs policy, strong encryption standards (such as AES-256), secure VPN protocols (like OpenVPN, IKEv2, or WireGuard), and additional privacy features like a kill switch and DNS leak protection.
Quick Links:
Conclusion: Does VPN Protect Your Online Privacy in 2024?
VPNs play a pivotal role in enhancing your online privacy by encrypting your internet connection and masking your IP address.
This makes it significantly harder for hackers, ISPs, and even governments to track your online activities. However, it’s crucial to remember that while VPNs offer a substantial level of protection, they are not a panacea.
The effectiveness of a VPN in safeguarding your online privacy also heavily depends on the provider’s policies, the strength of the encryption, and the legal jurisdiction under which the VPN operates.
Therefore, choosing a reputable VPN provider and staying informed about best practices in online privacy are essential steps in ensuring that your digital life remains secure and private.
Always complement the use of a VPN with other privacy-preserving measures to achieve the best possible protection for your online activities.






Hello Jitendra,
Online privacy is a big concern for users. Using a VPN service certainly helps you to keep yourself anonymous. I am also using ExpressVPN service. It helps me to keep myself secure. Thanks for sharing these helpful tips here.
Regards,
Vishwajeet