Oxylabs

- Fast and secure connections
- Large peer-to-peer network
- Residential and datacenter proxies
- Strong encryption and privacy
Decodo

- High-speed rotating proxies
- Reliable peer-to-peer network
- Easy setup and integration
- Multiple proxy types available
Webshare

- Affordable and private proxies
- Stable and anonymous browsing
- Unlimited bandwidth support
- Fast and secure connections
Want to jump straight to the answer? When it comes to Best P2P Proxy Providers, most individuals find Oxylabs and Decodo are the best options.
Are you looking for the best P2P proxy providers? Peer-to-peer (P2P) proxies are essential for secure and efficient data sharing, torrenting, and web scraping.
Whether you’re a casual user or a professional, finding the right P2P proxy can enhance your online activities while keeping your data safe.
In this article, I’ll list some of the Best P2P Proxy Providers, their features, and how you can use them in real life. You just have to keep reading.
What Is a P2P Proxy Network?
If you are a web expert, you presumably know a couple of things about how data goes around the web, yet you probably won’t know the entire story.
Seeing how data moves from one PC to the next over the World Wide Web will help you improve in the future.
That begins with understanding why a reverse proxy administration like this one is so stunning and how it provides you with the greatest measure of security.
A proxy server accesses the web on your behalf without your IP address being involved in the transfer.
The way the web typically works, your IP address is logged on almost every webpage you visit and when you download or transfer data.
Any sites you visit will realize you have been there, which pages you looked at, and for how long.
8 Best P2P Proxy Servers 2026
1. OxyLabs
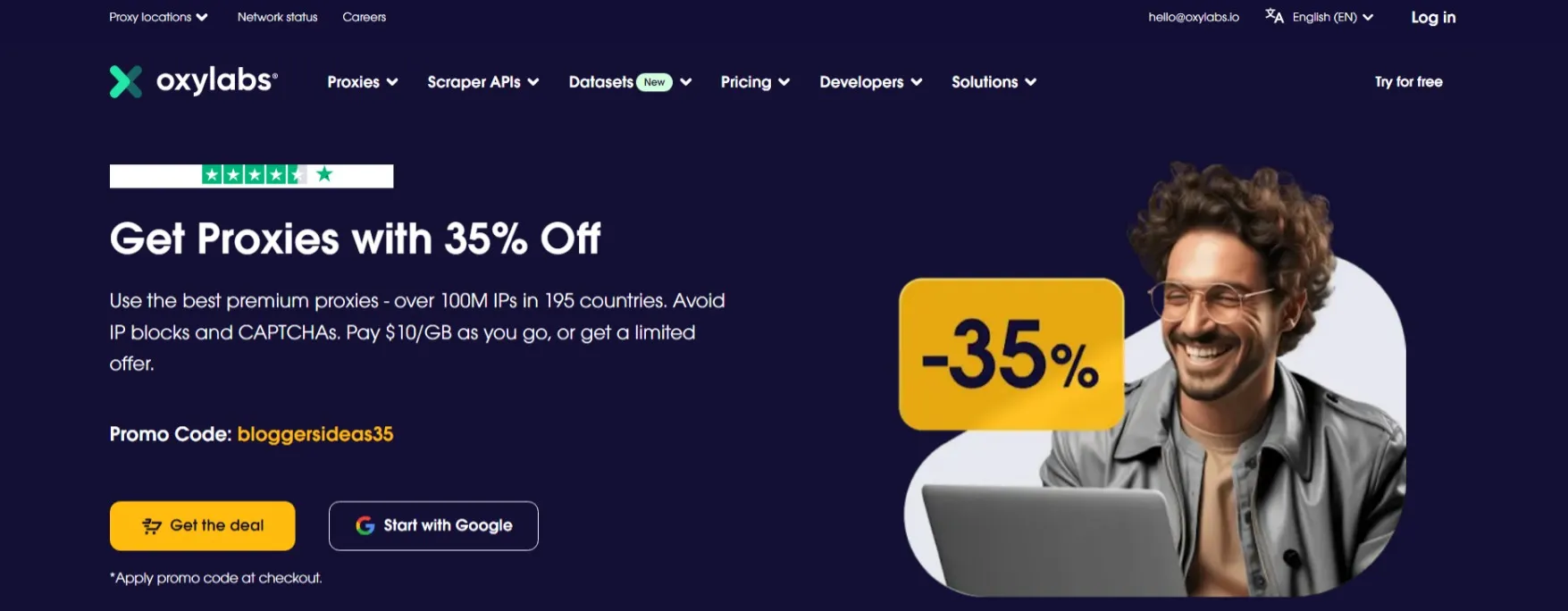
Oxylabs is one of the oldest and most reliable technology companies specializing in proxy servers. It essentially helps companies extract essential business data.
The best thing about Oxylabs is its pool of 175 million IP addresses and 10 million private IP proxy networks across more than 180 countries worldwide, which is quite impressive.
Oxylabs generally provides IP addresses for data centres and households that support HTTP / HTTP protocols and SOCKS® protocols. Let’s get information about the IP addresses of the data centre and the private proxy.
Datacenter IP: This IP address is usually assigned to a secondary company and is not owned by any Internet Service Provider (ISP).
Residential Proxy: This IP address is assigned to one of the owner’s standard Internet access providers (ISPs).
Oxylabs offers several notable features. Its in-house rotation system ensures optimal performance and reliability.
Multiple locations are available, allowing users to select the most suitable proxy server for their needs. Full IPV6 support ensures compatibility with the latest technology standards.
Additionally, Oxylabs offers custom setup options to provide tailored solutions for specific requirements.
Their 24/7 technical support ensures prompt assistance whenever needed, and their commitment to maintaining a 99% uptime ensures uninterrupted access to their proxy services.
One notable feature of Oxylabs is its lean IP management tool, which simplifies IP address management and organization.
This user-friendly tool enhances the experience and makes it easier to navigate and optimize proxy usage.
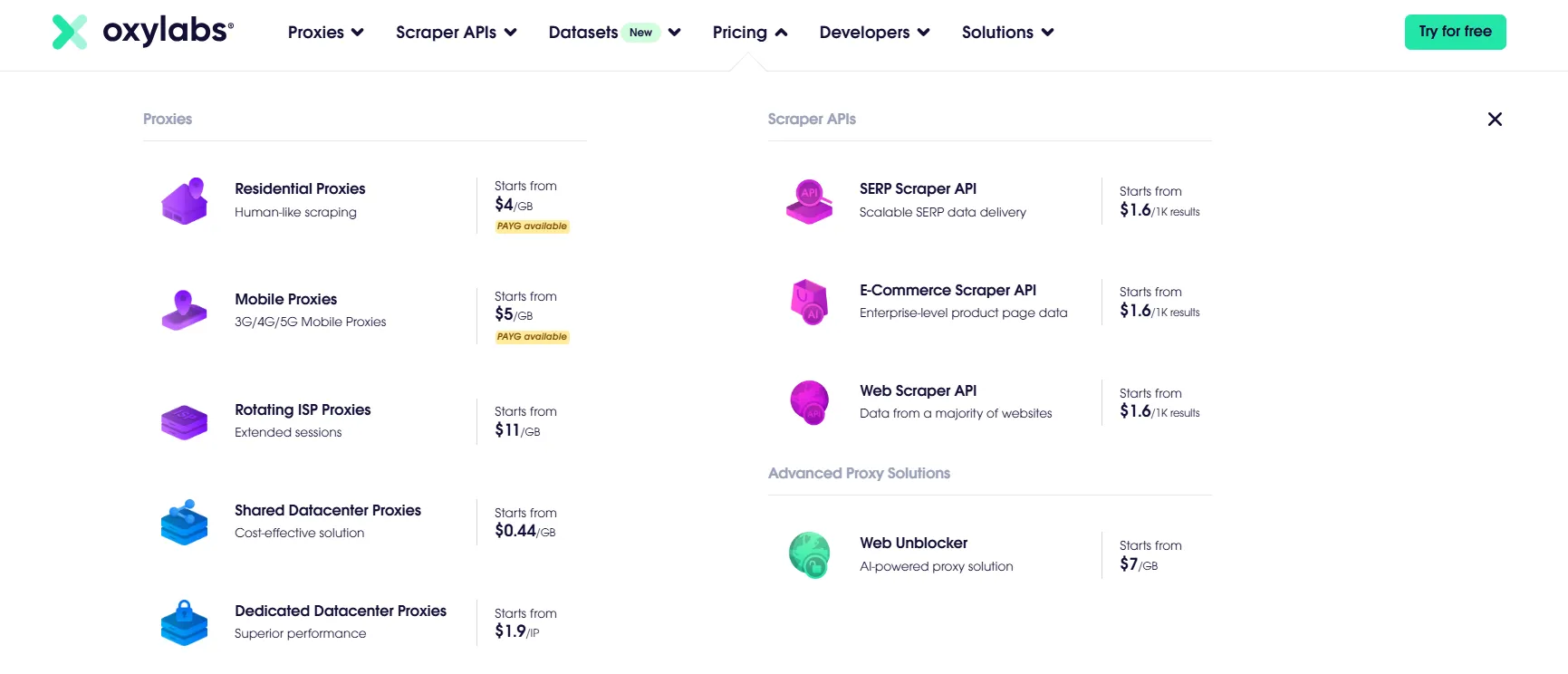
Oxylabs Pricing:
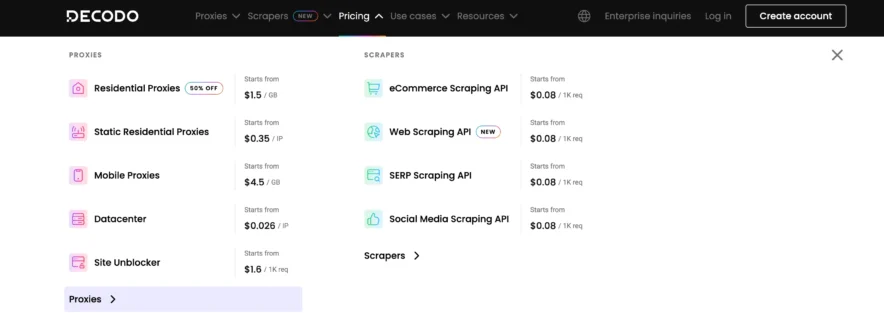
2. Decodo
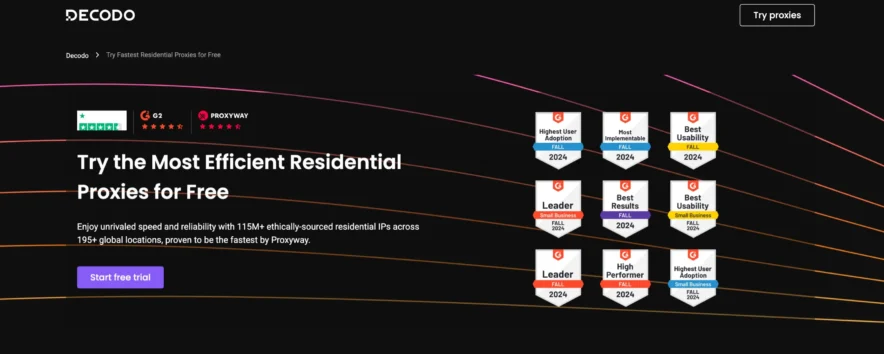
Decodo is one of the premium companies in the residential rotating proxy industry today.
Not only do they have over 125 million IP addresses that go through real mobile and desktop proxy networks in more than 195 locations worldwide, but they also offer unlimited connections.
One of the key advantages of Decodo is its unlimited connections. This means you can establish as many connections as needed, enabling efficient data extraction and seamless browsing.
Decodo offers a 14-day money-back guarantee and flexible pricing options. One option is a Pay-As-You-Go plan that starts at $1.50 per GB.
This allows users to purchase bandwidth without any monthly commitment. Additionally, Decodo offers a 3-day free trial that includes 100 MB of residential proxy data for new users.
Whether you’re a small business or a large enterprise, this flexibility allows you to scale your operations without limitations.
This is particularly useful for geographically restricted content or market research that requires data from specific regions. Their diverse IP pool enhances anonymity and helps bypass geo-blocking restrictions.
Decodo Pricing:
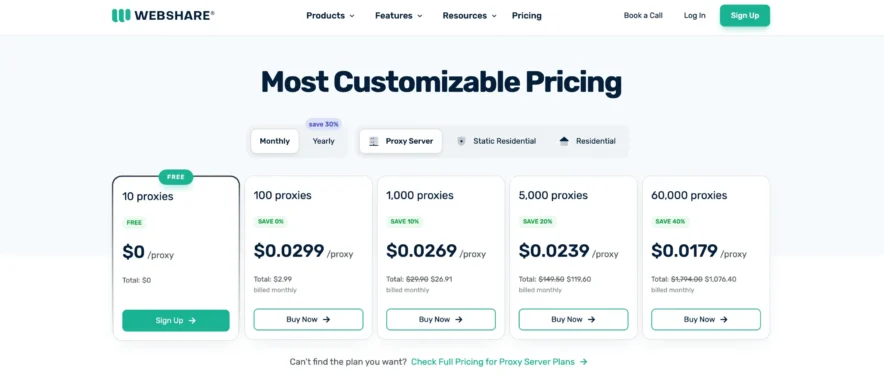
3. Webshare
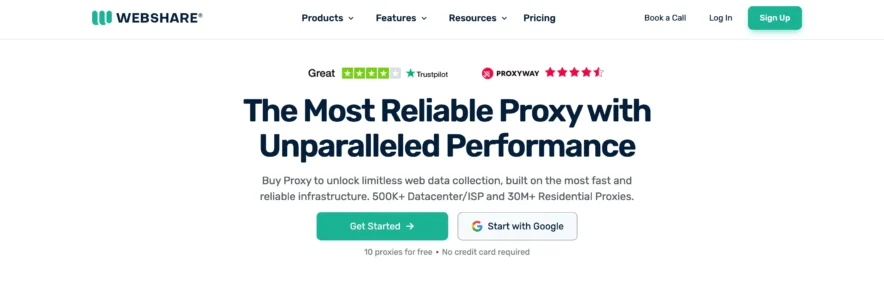
Webshare offers affordable and high-quality P2P proxies, ideal for secure browsing, web scraping, and anonymous data collection.
With a large network of rotating peer-to-peer (P2P) IP addresses, users can access geo-restricted content, bypass censorship, and ensure high levels of anonymity.
These proxies offer fast, stable, and reliable connections, making them ideal for businesses and individuals seeking efficient and undetectable proxy solutions.
Webshare’s customizable proxy settings enable users to optimize their proxy usage according to specific needs.
With a user-friendly dashboard and API integration, Webshare ensures seamless proxy management for all users.
Webshare Pricing:
4. Bright Data

Bright Data stands out as the premier P2P proxy provider, boasting a global pool of proxies that sets the standard in the industry.
Beyond merely offering proxy services, it goes the extra mile by providing comprehensive datasets and data collection solutions.
With a satisfied customer base exceeding 15,000 worldwide, Bright Data’s proxy solutions have earned unwavering trust.
Bright Data’s proxy services are trusted by Fortune 500 companies, institutions, and businesses, cementing its reputation as the go-to choice in the field.
One notable feature of Bright Data is its encryption of all traffic through a multitude of IPs using HTTP/HTTPS requests.
This encryption adds an extra layer of security to protect your data and ensure privacy while browsing or conducting online activities.
Additionally, Bright Data provides a free VPN service called Hola. This VPN operates similarly to Tor, routing your traffic through a network of computers or servers owned by Tor clients.
However, it’s important to note that using the free version of Hola might make you a potential proxy node for Bright Data’s users.
This arrangement enables Bright Data to leverage the extensive Hola network and expand its proxy capabilities.
The sheer size of Hola’s P2P network is remarkable, boasting millions of private residential IPs.
This extensive network reduces the likelihood of encountering IP blocks or detection, ensuring a smooth and uninterrupted proxy experience.
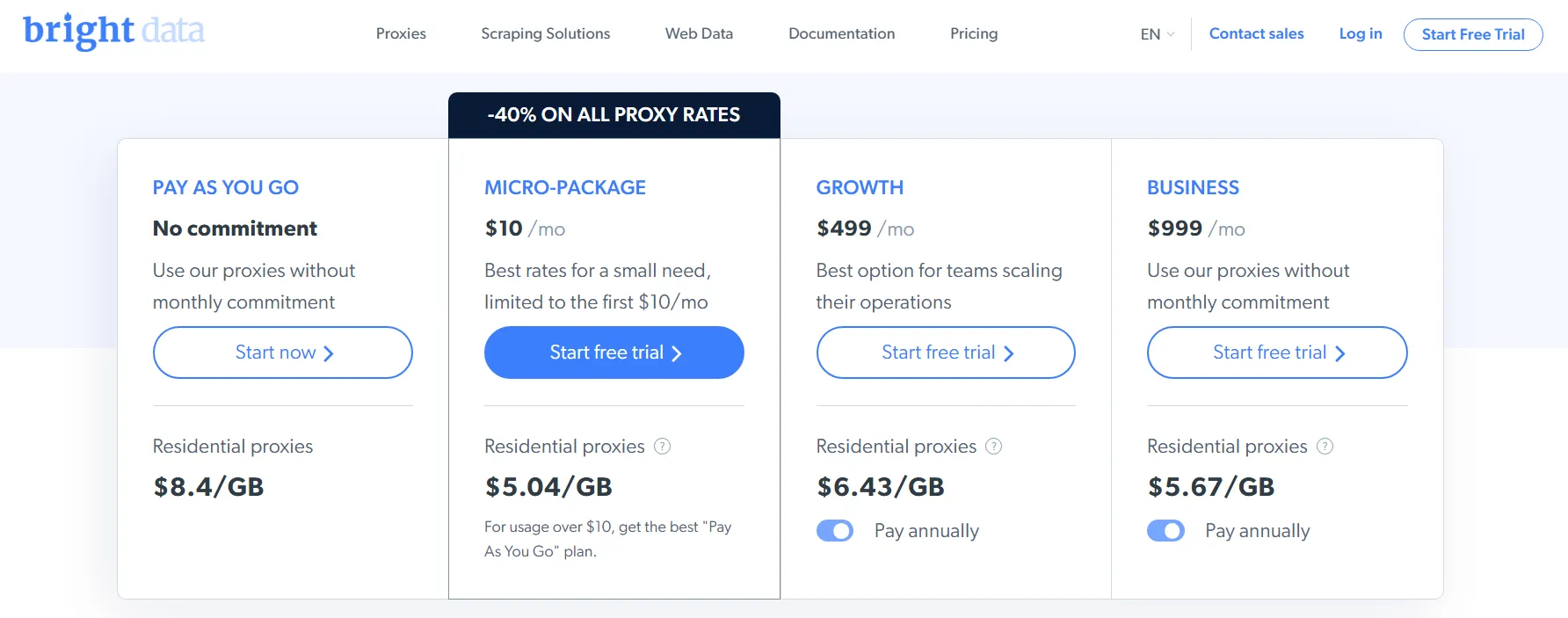
Bright Data Pricing:
5. Squid Proxies
Squid is a full-featured web proxy server application that provides proxy and caching services to HyperText Transport Protocol (HTTP), File Transfer Protocol (FTP), and other prevalent network protocols.
Squid can execute the reserving and proxying of Secure Sockets Layer (SSL) requests, store Domain Name System (DNS) queries, and perform straightforward caching.
Squid also supports a wide range of caching protocols, including the Internet Cache Protocol (ICP), the Hypertext Caching Protocol (HTCP), the Cache Array Routing Protocol (CARP), and the Web Cache Coordination Protocol (WCCP).
The Squid proxy server is an excellent solution for various proxy and caching server needs.
It can scale from branch offices to enterprise-level systems, providing extensive access control tools and monitoring essential parameters using the Simple Network Management Protocol (SNMP).
When choosing a PC framework as a dedicated Squid caching proxy server for some clients, ensure it is equipped with ample physical memory, as Squid maintains an in-memory cache for improved performance.
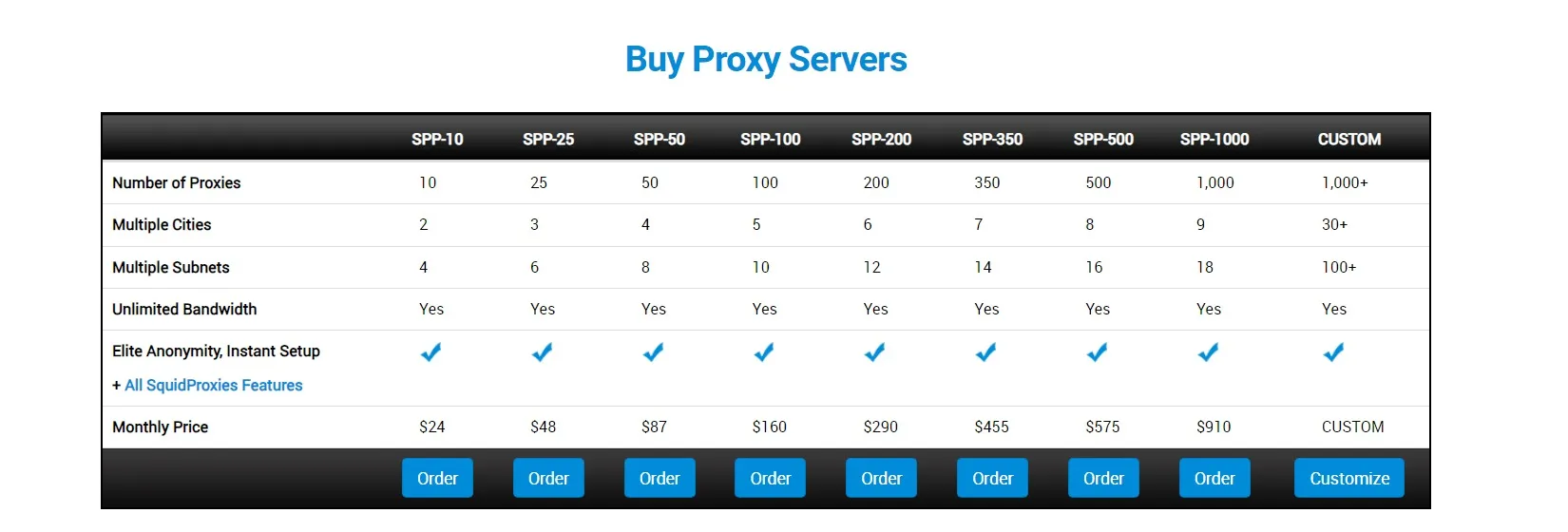
Squid Proxies Pricing:
6. Shifter
Shifter is another popular proxy network in the market. The Private IP is available in Shifter batches. All proxies come right with a 99.99% uptime.
They were able to handle the most difficult challenges of middle management.
With Shifter Unlimited and fast data transfer options, you will also have access to effective support groups for various proxies. It offers Shared Proxies and Backconnect Proxies.
Four services are offered: disconnect proxy, dedicated HTTP proxies, shared HTTP proxies, and automatic captcha resolution with independent plans and costs for each administration.
All locations are effectively open without geo-containment. Customer service is delivered tirelessly, which is quite impressive.
Shifter Pricing:

7. Oculus Proxies
Oculus Proxy is highly regarded for providing some of the best peer-to-peer (P2P) proxy servers available.
These P2P proxies are designed to handle large volumes of data transfer, making them ideal for activities such as file sharing, streaming, and other bandwidth-intensive tasks.
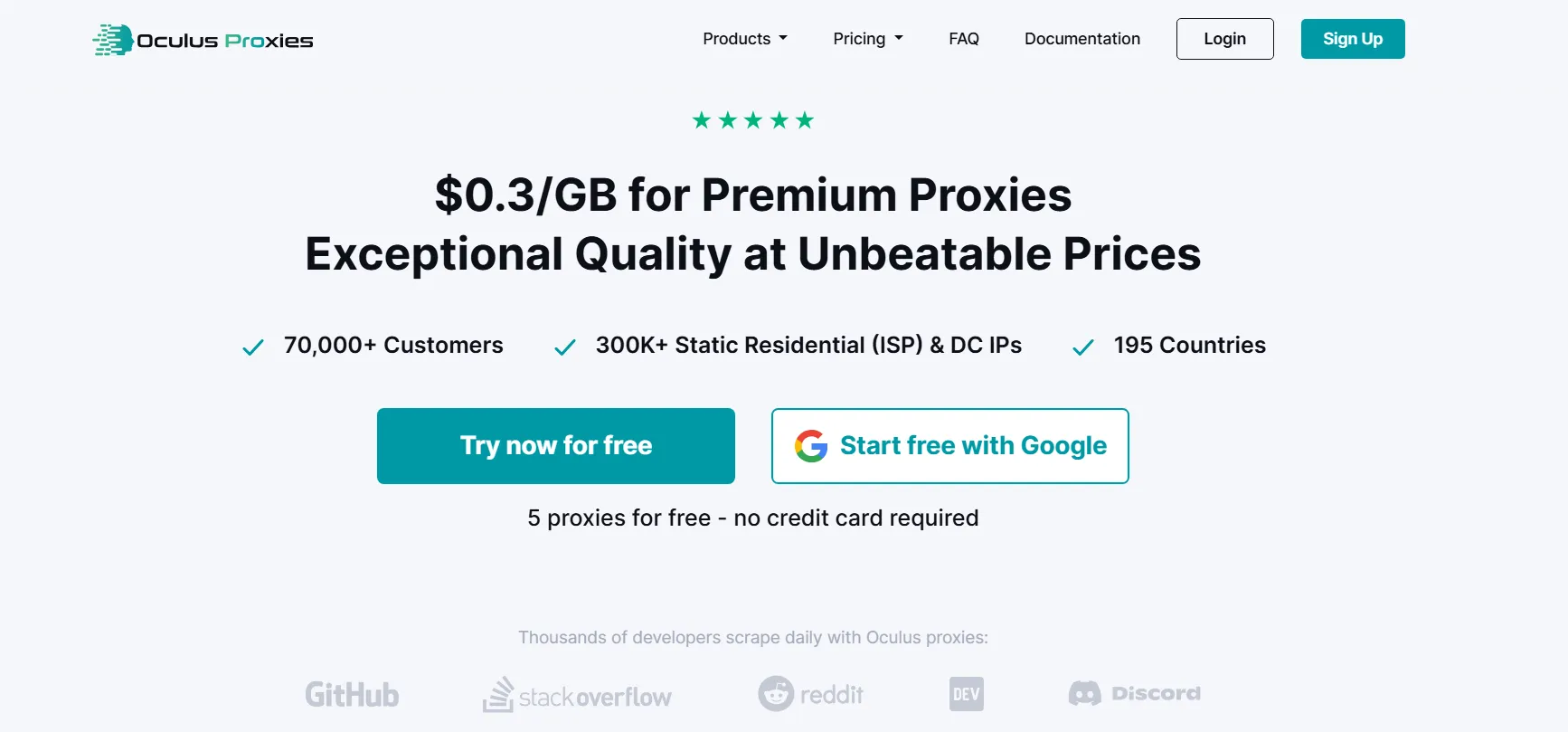
With Oculus Proxy’s P2P services, users can enjoy high-speed and reliable connections while maintaining their anonymity and security throughout their online activities.
Oculus Proxy’s P2P proxy servers are optimized for performance, ensuring that users experience minimal latency and fast data transfer rates.
This makes them particularly suitable for applications that require high bandwidth, such as downloading large files, streaming high-definition videos, and participating in decentralized networks.
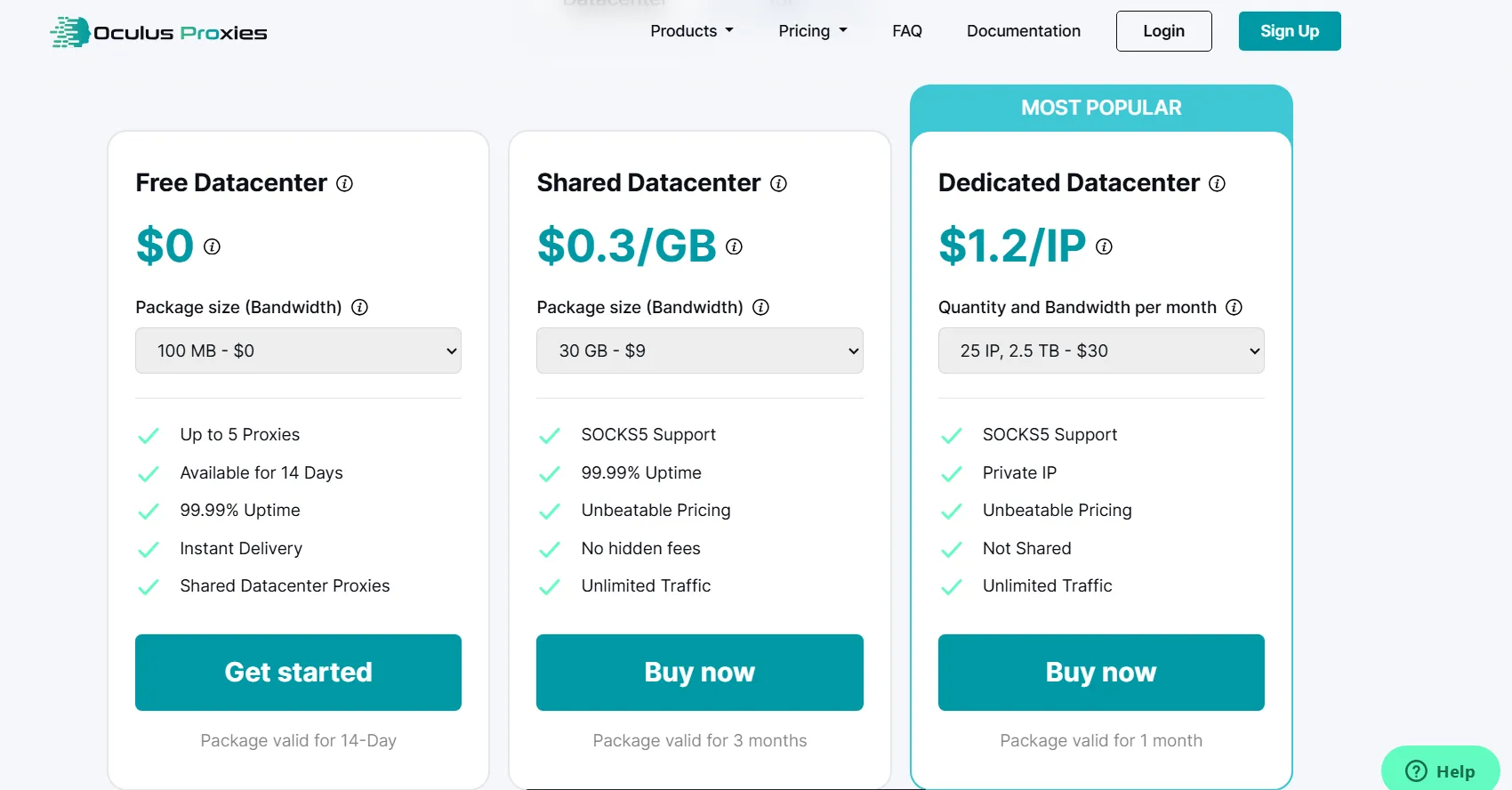
Oculus Proxies Pricing:
8. My IP Hide
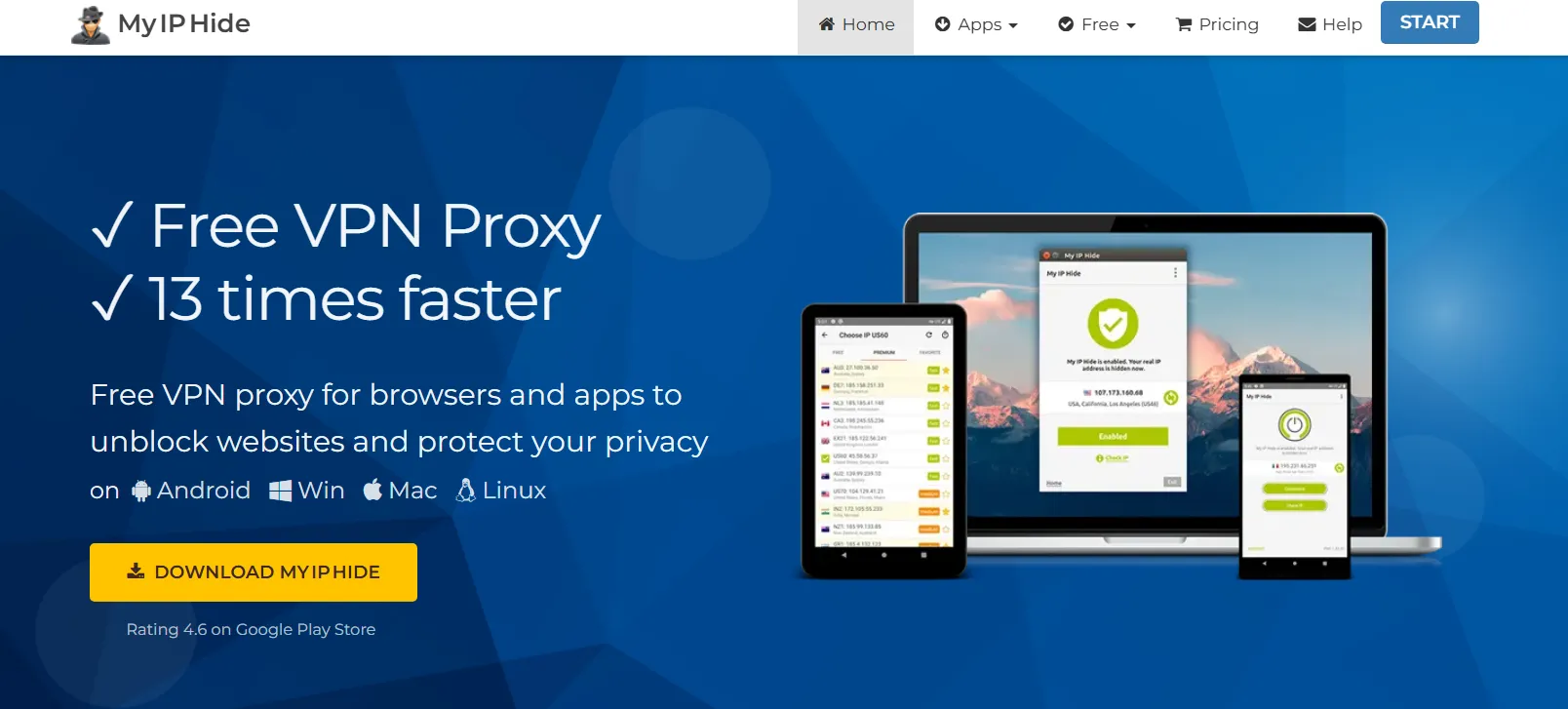
My IP Hide is a high-speed proxy service to unblock sites and conceal your genuine IP by encoding traffic. It is steady, quick, and simple to utilize.
With our upgraded proxy innovation, My IP Hide is significantly faster than other concealment IP solutions, such as VPN, SSH, and web proxy.
My IP Hide provides more secure, encrypted traffic, allowing access to various websites, including Facebook, Twitter, YouTube, Netflix, and BBC iPlayer, from anywhere, at any time.
Your record can be utilized on My IP Hide’s Windows, Mac, and Android forms.
You can say that free proxies are usually slow, unstable, and prone to dying quickly. Sometimes it takes too long to find new working proxies each day.
The product My IP Hide can save you time (and your life). It uses private proxy servers that are monitored and optimized to ensure they remain fast and reliable.
Security: Free proxies are available for open use. It makes them insecure, and they die quickly. On the other hand, My IP Hide is quick and stable in every case.
Encryption: Normal proxies don’t scramble their traffic. On the other hand, My IP Hide routes its traffic to bypass the most advanced firewalls.
In addition, My IP Hide is much faster than the VPN multiple times over. For more subtleties, you can peruse this test report. It changes IP addresses every minute, using 70 private proxies across 24 countries.
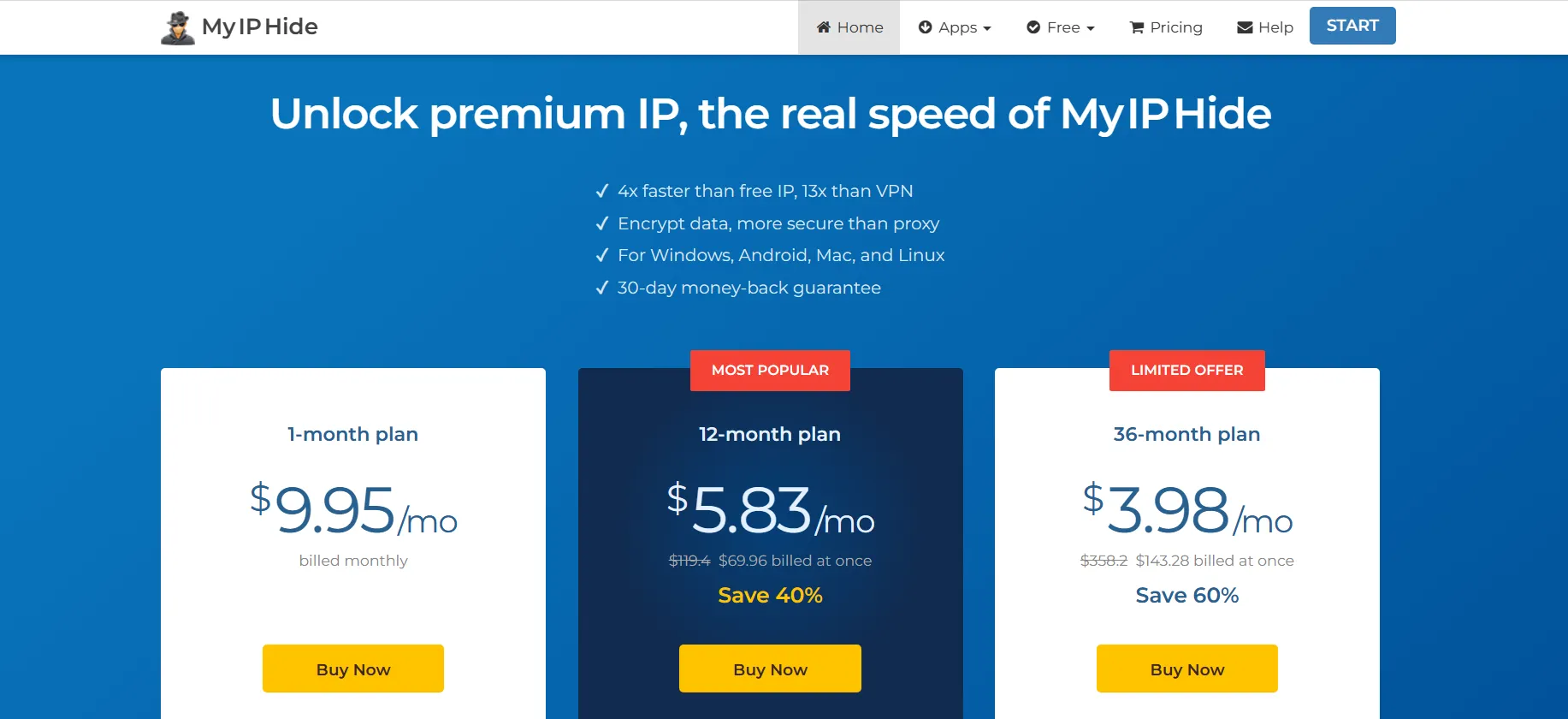
My IP Hide Pricing:
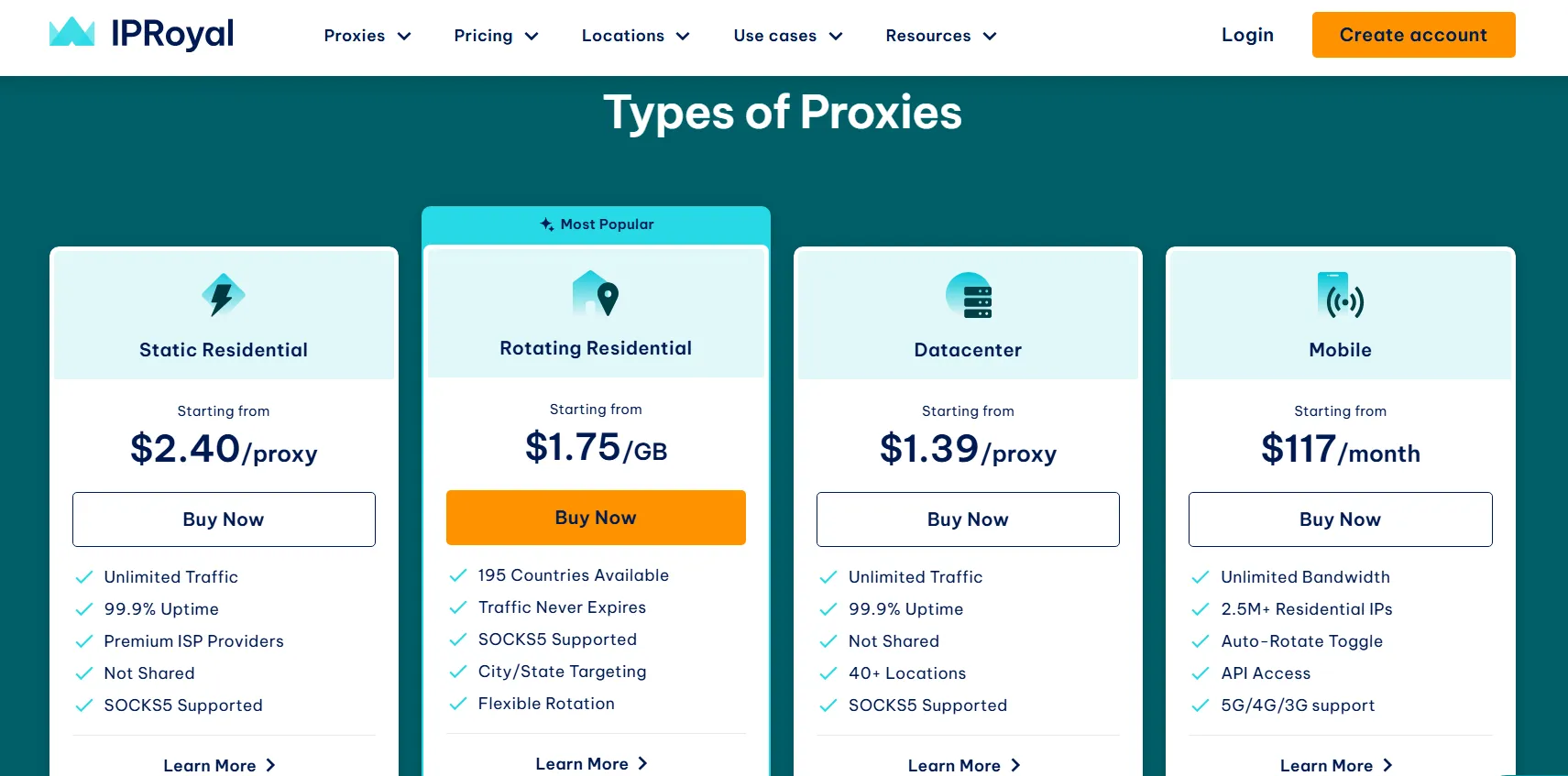
9. IPRoyal Proxy
They offer datacenter solutions with unlimited bandwidth, blazing speeds, and easy integration. You can pick from different locations worldwide.
With this service, you can be anonymous while surfing the internet anywhere in the world without worrying about geo-blocking or your private data being compromised.
Enjoy IPRoyal support for easy data extraction. It helps you be anonymous and safe. You can use it to learn more about your market, protect your brand, or add extra security to your infrastructure without any problem.
Whether you’re running a large-scale operation or a small business, their P2P proxy service keeps your sensitive information secure from prying eyes.
It’s remarkable how iProyal empowers individuals and businesses to navigate the online world with confidence. They offer a wide range of locations worldwide, allowing you to choose the proxy server that best suits your needs.
With iProyal, you’re not just getting a service; you’re gaining peace of mind and the freedom to explore the web without limitations.
If you’re looking for a P2P proxy provider that combines top-notch security, exceptional performance, and user-friendly integration, look no further than iProyal.
They’ve got you covered with reliable, feature-packed solutions. Step into the realm of online anonymity and enjoy the benefits that iProyal offers. Trust me, you won’t be disappointed!
IPRoyal Pricing:
FAQs
👍Which VPN is the fastest for P2P?
The fastest VPN for P2P depends on server location, network congestion, and your internet connection. ExpressVPN, NordVPN, and Surfshark are P2P-friendly VPNs.
🚀What is the best proxy for Torrenting?
SOCKS5 proxies are suggested for torrenting since they are quicker and more private. NordVPN, and IPVanish are torrenting SOCKS5 proxies.
👀Is there a free VPN that supports P2P?
Free P2P VPNs exist. Free VPNs sometimes have data constraints, slower connections, and less security and privacy than commercial VPNs. Windscribe and ProtonVPN are free P2P VPNs.
❓How do I choose the right P2P proxy provider?
Consider factors such as the size of the IP pool, pricing, customer support, and specific features like bandwidth limits and targeting options.
🤷♀️Are P2P proxies legal?
Yes, P2P proxies are legal for legitimate use cases such as web scraping for data analysis, market research, and accessing publicly available information.
Quick Links:
- ProxySeller Review
- Best Proxy Affiliate Programs
- Anonymous Proxies Review
- Brazy Proxy Alternatives
- ABC S5 Proxy Review
Conclusion: Best P2P Proxy Servers 2026
The P2P Proxy Network boasts numerous valuable features, but its most significant advantage is the ability to access servers anonymously.
You send information to one of their proxy servers on the other side, using a unique proxy server with an extraordinary IP address.
This means that your IP address is always changing. The P2P Proxy Network maintains approximately 1,000 to 2,000 active proxy servers at any given time, along with a pool of 10,000 servers that can be utilized as needed.
This makes the P2P Proxy Network the top anonymizer on the Internet.
I hope this post suits your purpose well. If you liked the post, you can share it on social media channels like Twitter, LinkedIn, and Facebook.